这期内容当中小编将会给大家带来有关Centos7中怎么利用DenyHosts防止ssh暴力破解,文章内容丰富且以专业的角度为大家分析和叙述,阅读完这篇文章希望大家可以有所收获。下载DenyHosts包[root@localhost
这期内容当中小编将会给大家带来有关Centos7中怎么利用DenyHosts防止ssh暴力破解,文章内容丰富且以专业的角度为大家分析和叙述,阅读完这篇文章希望大家可以有所收获。
下载DenyHosts包
[root@localhost ~]# wget Http://jaist.dl.sourceforge.net/project/denyhosts/denyhosts/2.6/DenyHosts-2.6.tar.gz安装DenyHosts
[root@localhost ~]# tar xf DenyHosts-2.6.tar.gz[root@localhost ~]# cd DenyHosts-2.6[root@localhost DenyHosts-2.6]# python setup.py install制作配置文件
[root@localhost DenyHosts-2.6]# cp denyhosts.cfg-dist /etc/denyhosts.cfg[root@localhost DenyHosts-2.6]# cp daemon-control-dist daemon-control[root@localhost DenyHosts-2.6]# chown root daemon-control[root@localhost DenyHosts-2.6]# chmod 700 daemon-control修改配置文件
将daemon-control中的#DENYHOSTS_CFG = "/usr/share/denyhosts/denyhosts.cfg"改为 DENYHOSTS_CFG = "/etc/denyhosts.cfg"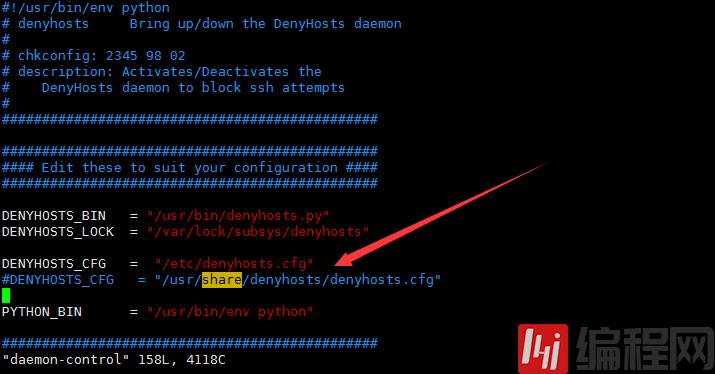
启动
[root@localhost DenyHosts-2.6]# ./daemon-control start(注意相对路径)默认允许五次,测试发现登陆失败五次之后不允许登陆
[root@localhost ~]# ssh abc@172.16.1.16abc@172.16.1.16's passWord: Permission denied, please try again.abc@172.16.1.16's password: Permission denied, please try again.abc@172.16.1.16's password: Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password).[root@localhost ~]# [root@localhost ~]# ssh abc@172.16.1.16abc@172.16.1.16's password: Permission denied, please try again.abc@172.16.1.16's password: Permission denied, please try again.abc@172.16.1.16's password: Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password).[root@localhost ~]# ssh abc@172.16.1.16abc@172.16.1.16's password: Permission denied, please try again.abc@172.16.1.16's password: Permission denied, please try again.abc@172.16.1.16's password: Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password).[root@localhost ~]# ssh abc@172.16.1.16abc@172.16.1.16's password: Permission denied, please try again.abc@172.16.1.16's password: Permission denied, please try again.abc@172.16.1.16's password: Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password).[root@localhost ~]# ssh abc@172.16.1.16ssh_exchange_identification: read: Connection reset by peer查看hosts.deny文件
登陆连续失败之后就会把ip地址写在hosts.deny文件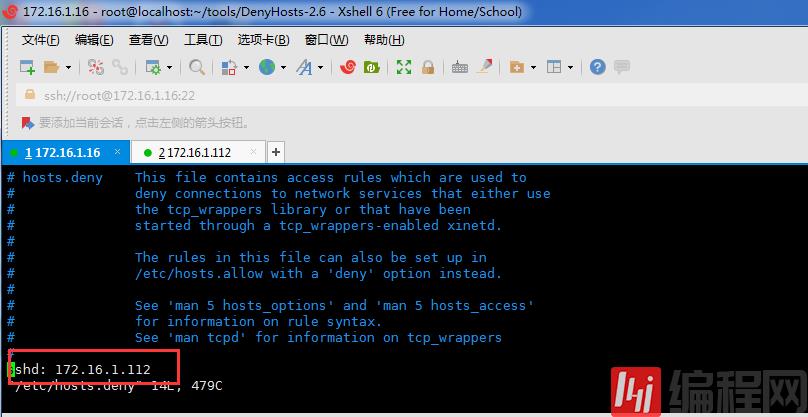
172.16.1.112的ip已经被限制,到此功能实现。
上述就是小编为大家分享的Centos7中怎么利用DenyHosts防止ssh暴力破解了,如果刚好有类似的疑惑,不妨参照上述分析进行理解。如果想知道更多相关知识,欢迎关注编程网精选频道。
--结束END--
本文标题: Centos7中怎么利用DenyHosts防止ssh暴力破解
本文链接: https://www.lsjlt.com/news/242736.html(转载时请注明来源链接)
有问题或投稿请发送至: 邮箱/279061341@qq.com QQ/279061341
下载Word文档到电脑,方便收藏和打印~
2024-05-24
2024-05-24
2024-05-24
2024-05-24
2024-05-24
2024-05-24
2024-05-24
2024-05-24
2024-05-24
2024-05-24
回答
回答
回答
回答
回答
回答
回答
回答
回答
回答
0